CamFlow
CamFlow
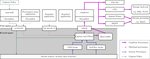
CamFlow stands for Cambridge information Flow architecture, the Cam is also the river that flows through Cambridge, UK. CamFlow is a Linux Security Module (LSM) designed to capture data provenance for the purpose of system audit. The whole-system provenance capture mechanism is highly configurable, and can fit the needs of many different type of applications. CamFlow can stack with existing security modules such as SELinux.
Thomas Pasquier
Assistant Professor
My research interests include provenance, operating systems, distributed systems and intrusion detection.
Related
Publications
Advanced Persistent Threats (APTs) are difficult to detect due to their low-and-slow attack patterns and frequent use of zero-day exploits. We present UNICORN, an anomaly-based APT detector that …
X Han,
T Pasquier,
A Bates,
J Mickens,
M Seltzer
System level provenance is of widespread interest for applications such as security enforcement and information protection. However, testing the correctness or completeness of provenance capture tools …
S C Chan,
J Cheney,
P Bhatotia,
A Gehani,
H Irshad,
T Pasquier,
L Carata,
M Seltzer
Valuable, sensitive, and regulated data flow freely through distributed governing the collection, use, and management of such data? We claim that distributed data provenance, the directed acyclic …
T Pasquier,
D Eyers,
M Seltzer
The Internet of Things promises a connected environment reacting to and addressing our every need, but based on the assumption that all of our movements and words can be recorded and analysed to …
T Pasquier,
D Eyers,
J Bacon
Identifying the root cause and impact of a system intrusion remains a foundational challenge in computer security. Digital provenance provides a detailed history of the flow of information within a …
T Pasquier,
X Han,
T Moyer,
A Bates,
O Hermant,
D Eyers,
J Bacon,
M Seltzer
Intrusion detection is an arms race; attackers evade intrusion detection systems by developing new attack vectors to sidestep known defense mechanisms. Provenance provides a detailed, structured …
X Han,
T Pasquier,
M Seltzer
Data provenance describes how data came to be in its present form. It includes data sources and the transformations that have been applied to them. Data provenance has many uses, from forensics and …
T Pasquier,
X Han,
M Goldstein,
T Moyer,
D Eyers,
M Seltzer,
J Bacon
We present FRAPpuccino (or FRAP), a provenance-based fault detection mechanism for Platform as a Service (PaaS) users, who run many instances of an application on a large cluster of machines. FRAP …
X Han,
T Pasquier,
T Ranjan,
M Goldstein,
M Seltzer